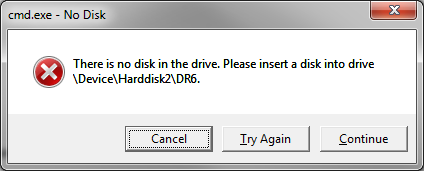
This morning a coworker logged in and was greeted with a dialog box he did not expect:
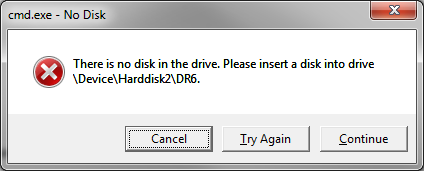 |
| There is no disk in the drive. Please insert a disk into drive \Device\Harddisk2\DR6. |
This was immediately suspicious. We quickly fired up Process Explorer to identify what could be causing the problem, and found a cmd.exe process that had been spawned by winlogon.exe, with the following command line:
“C:\Windows\System32\cmd.exe” /c echo [autorun]>>F:\autorun.ini
Alarm bells ringing! There’d be no reason a legitimate app would be trying to do this… F: is a card reader on my coworker’s machine, which he has never used, and hence is empty, which is why this message arose in the first place. He is running the most recent version of F-Prot, with up to date signatures, but that did not pick up this malware.
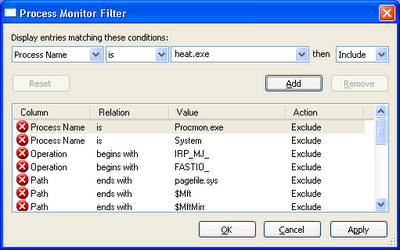
Now we knew there was something malicious afoot on his computer, we decided to try and capture as much information about the issue as possible. Unfortunately, we missed the first few steps that the virus was taking, and have no information on how it got onto to the computer in the first place, but here’s the rest of what we found.
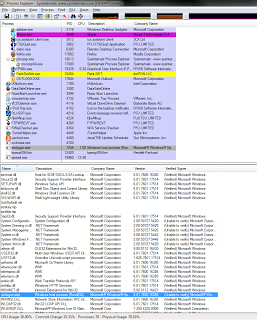
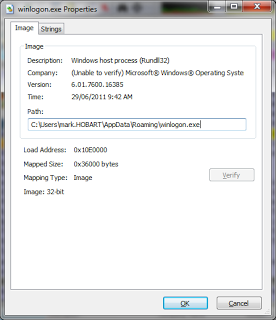
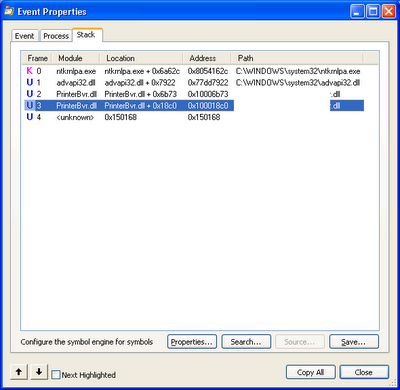
The first thing we spotted was that winlogon.exe had a version resource indicating it was created by Microsoft, but it also had no valid certificate, and the details were not consistent:
Curiously enough, we also spotted that it was a .NET application. I haven’t seen a .NET virus before… Looking at the process details, we could see it was running from %AppData%, which is certainly not kosher:
We took a look at the folder, and saw a couple of other files, spread.exe and MSNMessengerAPI.dll. Looks like it may spread through Windows Messenger?
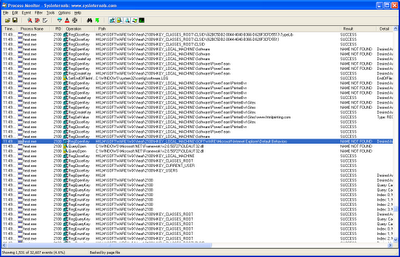
In Process Explorer, sure enough, spread.exe was running. Then something which was concerning: it appeared to be writing to what I believe is Firefox’s certificate database, accessing cert8.db and key3.db:
We also spotted a third process was spotted, svchosts.exe, which was stored in another folder: %LOCALAPPDATA%\Microsoft. It may not be related but seems to be similar in construction. This process was notable for a handle leak; at the time we spotted it, it had over 4700 handles open, mostly thread and duplicate file handles. Now it was time to kill the processes. I was expecting, given 3 processes, some complex watchdogging to prevent the processes being killed by the end user, but no, we were able to kill one after the other without any interference.
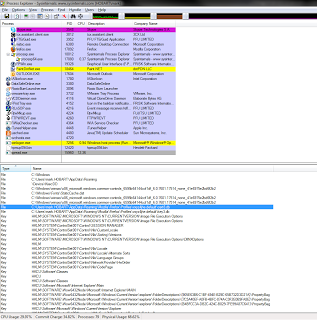
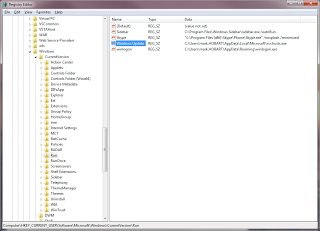
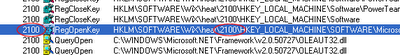
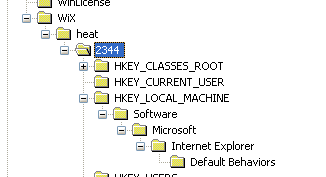
Now that there seemed to be no suspicious processes running, we took a look at the registry. It fairly naively installed itself into HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run.
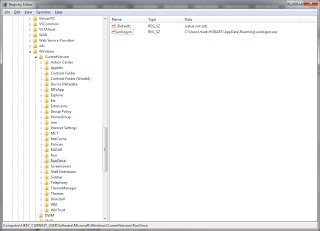
The HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\RunOnce key also contained a simple reference to winlogon.exe:
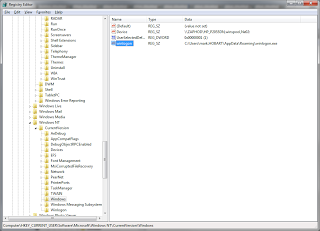
And curiously enough, HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows key had a reference to winlogon.exe as well:
At this stage, we zipped up the various virus files and deleted them, restarted, and so far, no residue has been detected. It appears that the virus did not manage to elevate itself and attain administrator access, which was reassuring.
Finally we ran the following SysInternals command to give us a rough idea of what winlogon.exe references:
strings -n 16 winlogon.exe
This command picked up function import references to sqllite3 and cryptography functions, which strengthened my fears about Firefox’s certificate store. Very few interesting strings were spotted, which suggests that they may have been encrypted. We opted to uninstall and reinstall Firefox, creating a new profile and all, but I remain concerned about whether or not Internet Explorer’s certificate store has been compromised.
We have not diagnosed how this virus spreads, but have submitted it to F-Prot for evaluation. I’ll be interested to see the outcome.